Blockchain technology is one of the novel technologies—the Fourth Industrial Revolution—that birthed ideas and revolutionized several industries. From the rise of Bitcoin in 2008 to its application in healthcare, the smearing effect of the blockchain is beyond doubt. In the simplest definition, blockchain is an immutable digital ledger shared across a network for processing transactions and tracking tangible and intangible assets.
Despite the blockchain’s innovation, it comes with tradeoffs, mainly observed with its security. A blockchain’s security is critical to open the growth and development room.
Cryptocurrencies being the face of blockchain technology alone, have suffered an ill fate due to cybersecurity pitfalls and threats that led to losses rounding at $9 billion from 500 cyber attacks. With the market’s potential drawing a bead of $1.43 trillion by 2030, developers need to know the security threats and how to mitigate them moving forward.
Understanding The Blockchain Structure
The blockchain has been primarily adopted by many individuals and businesses, mainly for its decentralized nature, adding trust and confidence in transactions. While the decentralized nature stands out as a key attraction, it’s necessary to identify the blockchain’s structure/architecture to determine possible threats, hazards, and, more importantly, the pointers to solving these security vulnerabilities.
The blockchain is divided into five (5) layers that form its backbone: hardware or infrastructure layer, data layer, network layer, consensus layer, and application layer. These layers all have their unique functionalities. And for a bad actor with malicious intent, attacking the blockchain is done on different layers; that is, the security breach can be done on any layer.
With each layer prone to specific vulnerabilities, unraveling how it works by shedding light on these different layers is necessary.
The Hardware/ Infrastructure Layer
The way the blockchain works, data are stored on servers. To access these data on servers, clients need to request it through an application layer. Similar to how you search for data through the internet.
Facilitating the data transfer between the client and server (client-server layer) is the peer-to-peer (P2P) network of nodes. These nodes are connected decentralized computers that record data on the blockchain and validate transactions. These nodes are physical devices; hence, the reason behind this layer’s name.
The hardware layer is the foundation of other layers of the blockchain. The common security vulnerabilities at this level include Information Leakage, uncle-block attacks, block discarding attacks, denial of service attacks, cross-domain phishing attacks, selfish mining, bribery attack, block withholding attack, and pool hopping attacks.
Data Layer
This is the data storage layer. Blockchains are made of blocks with data structures that are linked together; each of these blocks records data of transactions and is immutable and permanent. These blocks are made of six elements: version number, transaction data, timestamp, nonce, difficulty target, and a hash of the previous block.
To access the data stored on the blocks, a digital signature is required, which is made of private and public keys; the former signs the transactions, and the latter verifies the signer, that is, for encrypting and decrypting transaction data.
Some examples of security threats on this layer are cryptographic attacks, private key prediction, false top-up attacks, time-Locked transaction attacks, length extension attacks, transaction replay attacks, rug pull attacks, transaction malleability attacks, and hash collision attacks.
Network Layer
This layer is known as the propagation layer. The blockchain network comprises of nodes that communicate and transfer data to determine the validity of a transaction to be recorded on the network. The network layer is behind the inter-node communication and data synchronization and distribution. Without this layer, nodes won’t be able to communicate and ensure the validity of transactions on the chain.
The network layer is also subject to security attacks from malicious actors in space. Examples of network layer vulnerabilities are Sybil attacks, Eclipse attacks, timejacking, Denial of service attacks, BGP hijack attacks, Alien attacks, and Eavesdropping attacks.
Consensus Layer
This is one critical component of the blockchain. As the name suggests, the consensus layer is focused on ensuring the blockchain’s nodes agree to the validity of transactions to be recorded. This layer sets the seal on trust and confidence on the chain. Some refer to it as the protocol layer.
Different blockchains have the consensus they rely on; examples of these consensus layers include proof of work (PoW), Proof of Stake (PoS), Proof of History (PoH), Proof of Capacity (PoC), etc. Blockchain, such as Bitcoin, uses Proof of Work (PoW), and Ethereum relies on Proof of Stake (PoS), the widely adopted consensus mechanism.
The security threats discovered in this layer are long-range attacks, race attacks, 51% attacks, coin age accumulation attacks (double block production), grinding attack, alternative historical attack, Finney attack, liveness denial, vector76 attack, and censorship.
The Application Layer
This layer of the blockchain is the layer clients—users and developers—get to interact with the blockchain. This includes decentralized applications (dApps), smart contracts, interfaces, application programming interfaces (APIs), and software that run on the layer.
This layer is divided into two parts, the application, and execution layer. The application layer is the interactive part and programs users use in communicating with the blockchain; examples are the user interface, application programming interfaces (APIs), etc.
The execution layer works in hand with the application layer. The former sends instructions to the execution layer, which puts them into effect. A typical example will be a user’s action on a dApp—application layer— sent as an instruction to the execution layer, which enacts them. Examples of the execution layer include smart contracts and chaincodes.
Top Ten Blockchain Security Threats to Watch Out For
While there are lots of security threats and vulnerabilities in the blockchain, understanding each of these menaces will reduce the tendency for falling prey to them and help developers tackle them successfully. However, particular one’s standards out which are explained in detail below.
1. 51% Attack
2. Sybil Attack
3. Phishing Attack
4. Long-Range Attack
5. Grinding Attack
6. Rug pull attack
7. Private keys Atttack
8. Information Leakage
9. Timejacking
10. Censorship
51% Attack
The 51% attack is a consensus attack that occurs on a proof of work (PoW) consensus. Before transactions on a blockchain network are approved and accepted as valid, more than 50% of the nodes on the network need to agree on such transactions. This gives a sense of how the name 51% was derived and, in other cases, called the majority attack.
When more than 50% of the nodes are controlled by a miner or group with bad intent, they timely introduce a new but substitute blockchain to the existing blockchain or might erase a previously verified transaction from the blockchain. Beyond adding recent transactions to the block, it leads to double spending problems, AKA counterfeiting. In a 51% attack, reversing transactions that occurred long ago is very difficult.
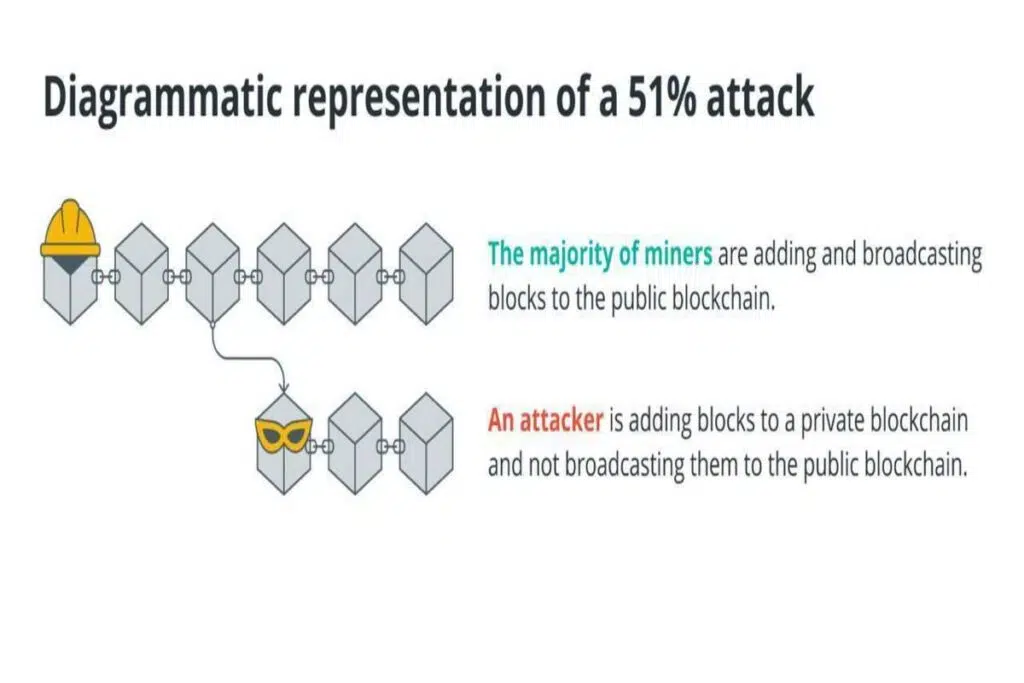
Controlling over 50% of nodes means the miners oversee a large portion of the network’s mining hashrates. Coordinating this attack type is expensive; they’re mainly observed on blockchains with lower hashing power. Successful counterfeiting has been witnessed with platforms like Ethereum Classic (ETC) and Litecoin Cash (LCC).
Sybil Attack
This is a type of network vulnerability attack. This type of attack on the blockchain occurs when a bad actor creates multiple nodes on the network to outrun legitimate nodes. If successfully carried out, it leads to a 51% attack explained above, hence tainting the blockchain’s reputation.
The word ‘Sybil’ was derived from the name of a woman, ‘Sybil Dorsett,’ who suffered from ‘Dissociative Identity Disorder,’ this medical condition caused her to take on multiple personalities. The term became popularized after being discussed in a Microsoft paper by John R. Douceur.
There are a few approaches to prevent Sybil attacks, including:
Identity validation: where the true identity of participants is requested. This might be through direct or indirect means.
Economic cost: requires users to commit to participating as a node, which can be staking crypto. This approach makes it expensive for a Sybil attack to occur. The proof of stake (PoS) consensus ensures this is possible. Depending on the consensus, there are different approaches to implementing economic cost.
Phishing Attacks
Phishing attacks are some of the most prevalent in the cryptocurrency arena. In 2022, some holders of the Bored Ape Yacht Club’s NFT lost $2.5 million to this attack.
This morning, the official BAYC Instagram account was hacked. The hacker posted a fraudulent link to a copycat of the BAYC website with a fake Airdrop, where users were prompted to sign a ‘safeTransferFrom’ transaction. This transferred their assets to the scammer's wallet.
— Bored Ape Yacht Club (@BoredApeYC) April 25, 2022Here, attackers hide under the identity of a recognized organization or person to swindle unsuspicious users of the blockchain, collecting information such as their private key or prompting them to take certain actions by clicking a malicious link.
This rampant infrastructure vulnerability requires users to be more vigilant to prevent this attack. Another approach to solving this will be using malicious link detector software that prevents cross-domain access.
Long Range Attack
This is a form of security vulnerability that occurs on proof of stake (PoS), and it’s very similar to a 51% attack but more threatening. Here, the attacker finds a way to create a substitute chain on the existing blockchain that eventually overrides the ledger to benefit them.
Long range attack on PoS is a more complex situation compared to the 51% attack because attackers can go further back in the blockchain’s history, like 60,000 blocks back; unlike the latter, attackers can’t go as far due to the difficulty associated with proof of work.
Attackers tampering with transactions on the chain as far back creates double spending problems. In contrast, a 51% attack finds it difficult to go beyond a certain block level, say six blocks, due to the difficulty and intensive work needed on proof of work consensus.
This problem exists when the proof of stake isn’t appropriately implemented, and attackers have a sizable number of tokens. There are two solutions to this problem: identity validation and slashing.
Grinding Attack
This type of attack occurs when a node on the blockchain influences the chain’s randomness into selecting them as the validator for the next block through computation and combining several parameters.
This creates an unfair gap, and it’s achieved when nodes skip a previous block to benefit from a much larger reward associated with validating a future block.
There are a couple of ways to solve this: nodes making an advance deposit, ensuring the blockchain avoids using easy-to-manipulate data to generate randomness, secret sharing or deterministic threshold signature, and cryptoeconomic schemes that require validators to publish certain information.
Rug pull attack
This is a network vulnerability attack, and it’s observed year in and out in the crypto arena. This one pan out when major token holders remove the liquidity by selling their tokens, leaving holders with little hope of recovery.
This type of attack renders a token useless, and it’s seen to happen on DeFi tokens, such as meme coins that haven’t been listed on licensed and recognized centralized exchanges such as Binance.
Rugpulls are so dangerous, and they need to be avoided at all costs, which can be done through in-depth research about a token before investing in it.
1/2 North Korea’s Lazarus Group had a very busy weekend moving $63.5m (~41000 ETH) from the Harmony bridge hack through Railgun before consolidating funds and depositing on three different exchanges. pic.twitter.com/huDumaJeSh
— ZachXBT (@zachxbt) January 15, 2023Private keys Attack
This remains one of the riskiest types of hacks ever. Private keys are a string of characters such as binary codes and mnemonic phrases that gives the right of ownership to crypto assets as well as completing transactions on the blockchain.
A private key attack is a type of data vulnerability that permits attackers to sign transactions on the blockchain without the consent of real owner.
This attack occurs when an attacker predicts a user’s private key or steals it from the unsuspecting user. The solution requires safeguarding their private keys and using a pseudorandom number generator.
Information Leakage
This type of hack is as straightforward as the name. It materializes when an attacker monitors the blockchain network to derive private information that can be used to comprise the system to its advantage. Sometimes, it’s referred to as eavesdropping.
Although this is considered a low-risk infrastructure layer attack, a more robust encryption protocol must be implemented on the blockchain to wave off any potential hacks on this layer.
Timejacking
This is a precarious and well-organized network layer vulnerability. Here, the attacker manipulates the timestamp of a node, making it unable to participate in validating transactions (as the time doesn’t correlate) with other blockchain nodes. Instead, it is forced to validate substitute blocks created by attackers.
This is temporary as the timestamp of the victim node is corrected after a while. It leads to a fork in the blockchain network and raises the problem of double spending.
Timejacking can be avoided by declining acceptance time ranges and relying on the node’s system time.
Censorship
This type of protocol vulnerability is directed to impede the decentralized nature of the blockchain. Censorship occurs if a transaction isn’t approved to be added to the blockchain ledger, which is influenced by a pause or stop in the chain.
Blockchain, found to be more vulnerable to censorship, operates on a small network of nodes or tends to be faster and cheaper. Solana and Binance Smart Chain are two examples. The case of the Binance Smart Chain is a little more complex as a central authority [Binance] controls it, lowering the network’s censorship resistance. If the identity of who’s transacting is revealed, censoring might be observed, which defeats the purpose of decentralization.
Different approaches to solving this include increasing the network nodes, Implementing Zero-knowledge (ZK), safeguarding the identity of those transacting, and punishing offender nodes.
Conclusion
Although the blockchain is innovative, it’s vulnerable to specific security threats. Developers must note these threats and the part of the blockchain architecture they’re associated with to tackle them effectively. In addition, continuous education, ongoing monitoring, and security audits are essential for tighter security on the blockchain.