Do you want to learn more about DeFi and sandwich attacks? Do you want to know how they work, how they affect you, and how you can avoid them? If yes, then you are reading the right article. This article explains everything you need to know about DeFi and sandwich attacks simply and easily; what they are, how they work, how much damage they have caused, and how you can prevent or avoid them. Read on and discover the over $20 million problem of sandwich attacks in DeFi.
- Introduction to Sandwich Attacks in DeFi
- What Are the Factors That Enable Sandwich Attacks in DeFi?
- Blockchain transparency and the mempool (how blockchain networks work)
- Gas fees and transaction priority (how much you pay for your trades)
- Price slippage and liquidity pools (how DEXs set their prices)
- What are some examples of sandwich attacks in DeFi?
- What are some ways to prevent or avoid sandwich attacks in DeFi?
- Using limit orders and stop-loss orders
- Using DEXs with better price oracles
- Using tools and protocols that hide your trades
- What Are Some Prominent DeFi Projects Vulnerable to Sandwich Attacks?
- Conclusion
Sandwich attacks cheat DeFi users by changing token prices on blockchain networks and DEXs. They make users pay more or get less for their trades, while they keep the profit. Users can avoid them by using limit orders, stop-loss orders, better-priced oracles, and privacy tools.
Introduction to Sandwich Attacks in DeFi
DeFi, short for decentralized finance, is simply a range of applications and platforms that use blockchain technology and smart contracts, or more simply put, they are like the computers and the internet used to render financial services without banks or other middlemen. DeFi lets users lend, borrow, trade, save, invest, and more in a way that is transparent, permissionless, and trustless or secure. DeFi is cool because it can help anyone with an internet connection and a crypto wallet to access financial services anywhere in the world.
But like many other financial systems, DeFi is not perfect. It has some problems and costly risks that you need to know about. One of these problems is called sandwich attacks. Sandwich attacks are a way of cheating people who use DeFi to trade tokens. Tokens are like digital coins that have different values and uses. For example, ETH is a token that you can use to pay for interacting with the Ethereum network, which is where most DeFi apps run.
Sandwich attacks happen when someone sees your trade and tries to make money from it by changing the price of the token you want to buy or sell. They—do this, by placing two trades around your trade: one before and one after. They make your trade look like a sandwich filling between two slices of bread, hence the dubbed name “Sandwich attacks”. This way, they can buy the token for cheaper or sell it for more than you do, and pocket the difference as their profit.
In recent years, sandwich attacks have caused a lot of damage in DeFi, especially on platforms that let users swap tokens directly from their wallets. These platforms are called decentralized exchanges or DEXs. According to some researchers, sandwich attacks have taken over $20 million from DeFi users between September 2020 and March 2021. The study also found that sandwich attacks account for over 22% of the total transaction fees paid by DeFi users during that period.
Read this guide to learn all you need to know about decentralized exchanges (DEXes).
What Are the Factors That Enable Sandwich Attacks in DeFi?
Sandwich attacks depend on three main factors: blockchain transparency and the mempool, gas fees, and transaction priority, and price slippage and liquidity pools— how DEXs set their prices.
Blockchain transparency and the mempool (how blockchain networks work)
Public blockchain networks are like ledgers that record all the transactions that happen on them. Anyone can see the transactions that are sent to the network. However, not all transactions are confirmed right away. Some transactions are waiting in a pool of unconfirmed transactions, called the mempool until they are included in a block by a miner. The mempool is also public, meaning that anyone can see the waiting transactions, and their details, such as who is sending, or receiving what—and how much they are paying for it. This allows attackers to watch the mempool for profitable opportunities to sandwich.
Gas fees and transaction priority (how much you pay for your trades)
When you send a transaction to a blockchain network, you have to pay a fee to get it confirmed. That fee you pay is called the gas fee, on Ethereum. Gas fees depend on how complex your transaction is and how busy the network is. You can choose to pay higher or lower gas fees depending on how fast you want your transaction to be confirmed, i.e., the higher the money, the faster the deal! Miners prefer transactions with higher gas fees because they earn more from them.
This creates an incentive for sandwich attackers to pay higher gas fees than you to make sure that their trades are confirmed faster before and after yours. That’s the whole idea of sandwich attacks, trying to be a step ahead.
Price slippage and liquidity pools (how DEXs set their prices)
Price slippage is the difference between the expected price and the actual price of a trade. Price slippage occurs when there is not enough liquidity in the market to fill an order at the desired price that the user is willing and able to pay, Liquidity is the availability of tokens for trading. DEXs use smart contracts to hold tokens from different users who provide them in exchange for fees or rewards. These smart contracts are called liquidity pools. DEXs use liquidity pools to determine the prices of tokens based on supply and demand.
When a big trade is made, it can affect the balance of the liquidity pool and change the price of the tokens. What this does is that I immediately create an opportunity for attackers to change the prices by placing trades before and after yours. That becomes a loophole in the system for attackers to manipulate and cash out on unsuspecting users.
What are some examples of sandwich attacks in DeFi?
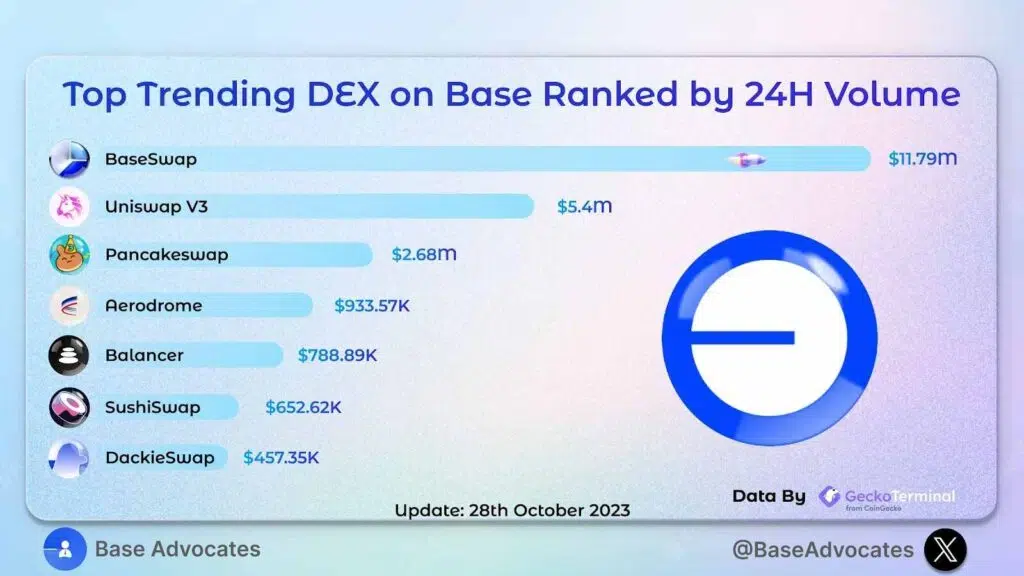
Sandwich attacks have happened on many DEXs in DeFi, such as Uniswap, Bancor, SushiSwap, and a couple of others. These platforms utilize automated market makers (AMMs) to provide liquidity and establish pricing for token exchanges. Here are some examples of sandwich attacks that have happened on some of the platforms:
The $EWT sandwich attack on Uniswap:
According to a verified X handle, someone lost 12 $EWT buying 200 $EWT in a sandwich attack for $EWTB on Uniswap, in October of 2022. This attack was confirmed by other users, stressing the quick adjustment of slippage to maybe 0.1%, as a mitigation measure.
MEV bot Sandwich Attack
In a supposedly breaking news by another verified X account, BitcoinWorld Media, the Ethereum Foundation lost $9,101 in MEV bot sandwich attack during a 1,700 ETH sale on Uniswap V3. MEV bot’s net profit hit a sum of $4,060. The account reported that the Sandwich attack disrupted the Mempool transactions, and gave the attacker room to sandwich the trade.
Many other instances of sandwich attacks on different platforms exist to date— too numerous to mention.
What are some ways to prevent or avoid sandwich attacks in DeFi?
Sandwich attacks are hard to stop completely, and this is because they are part of how blockchain networks and DEXs work. But, there are some ways that you can reduce the chance or impact of sandwich attacks in DeFi, if and when they happen. Some of them include, but are not limited to:
Using limit orders and stop-loss orders
Limit orders and stop-loss orders are types of trades that let you set the maximum or minimum price that you are willing to pay or receive for a token. Limit orders and stop-loss orders can help users avoid paying more or getting less than they want for their trades, as they will not execute if the market price is bad or unfavorable for the user. Some DEXs, such as 1inch and dYdX, let you use limit orders and stop-loss orders as features or integrations on their platform platforms.
Using DEXs with better price oracles
Price oracles are services that give reliable and accurate information about the market prices of tokens. Some DEXs, like Curve and Balancer—use price oracles to adjust their—liquidity pools and prevent big price differences from other markets. This can help you avoid losing too much money because of price slippage thus making it harder for sandwich attackers to change the prices. This also makes sandwich attacks unprofitable.
Using tools and protocols that hide your trades
This is one important, recommendable measure a user can put in place against attacks. Privacy-enhancing tools and protocols or tools and protocols that hide your trades are solutions that try to make your transactions more private and secret on blockchain networks. Some examples of tools and protocols that provide anonymity and confidentiality for users’ trades include Tornado Cash, Aztec Protocol, and zkSync. These solutions can help users hide their transaction details from sandwich attackers and stop them from watching the mempool for sandwich opportunities.
What Are Some Prominent DeFi Projects Vulnerable to Sandwich Attacks?
The truth is, any DeFi project that allows for direct trading of tokens (i.e. Decentralized Exchanges or DEXs, as earlier pointed out) can potentially be exposed to sandwich attacks. This includes well-known projects like Uniswap, PancakeSwap, or SushiSwap on the Ethereum network, and a host of others.
It is, however, very important to add that these projects are aware of the issue and are constantly working on ways to prevent such attacks from happening or repeating themselves. For example, they might use better price oracles (which are like price feed services), limit orders, stop-loss orders, and privacy tools as security measures, as highlighted in this article.
Conclusion
Sandwich attacks are a serious problem in DeFi that can affect anyone who uses DEXs to trade tokens, especially for crypto newbies and enthusiasts. Sandwich attacks exploit the way transactions are seen, paid, and priced on blockchain networks and DEXs to manipulate prices and make money from unwitting users. Sandwich attacks have caused over $20 million from DeFi users in less than a year, in the recent past.
But sandwich attacks are not impossible or unstoppable. Crypto novices or experienced users can take some measures to protect themselves from sandwich attacks, such as using limit orders, stop-loss orders, better-priced oracles, and tools that hide your trades. Users can also educate themselves about the risks and benefits of DeFi and do their research before using any DeFi application.